dinCloud Blog

The Significance of Application Security and How to Do it Right
In recent years, the world has been taken over by technology and remote work. As a result, applications and software have become integral to business
A DaaS v/s VDI Comparison – Which Solution is Best for Your Enterprise?
At first glance, it may seem like Virtual Desktop Infrastructure (VDI) and Desktop as a

List of Top 6 Best Desktop as a Service DaaS Providers 2023
Desktop as a Service (DaaS) is a type of Virtual Desktop Infrastructure (VDI), where a third-party service
How to Setup an Effective Cloud Detection and Response (CDR) Mechanism?
Cloud Computing architectures and environments have consistently been replacing legacy, on-premise IT infrastructures. This mass-scale
The Pivotal Role of IT Infrastructure Automation in Enterprise Operations
We have lately witnessed a mind-boggling scale and pace of digital transformation across enterprises. The
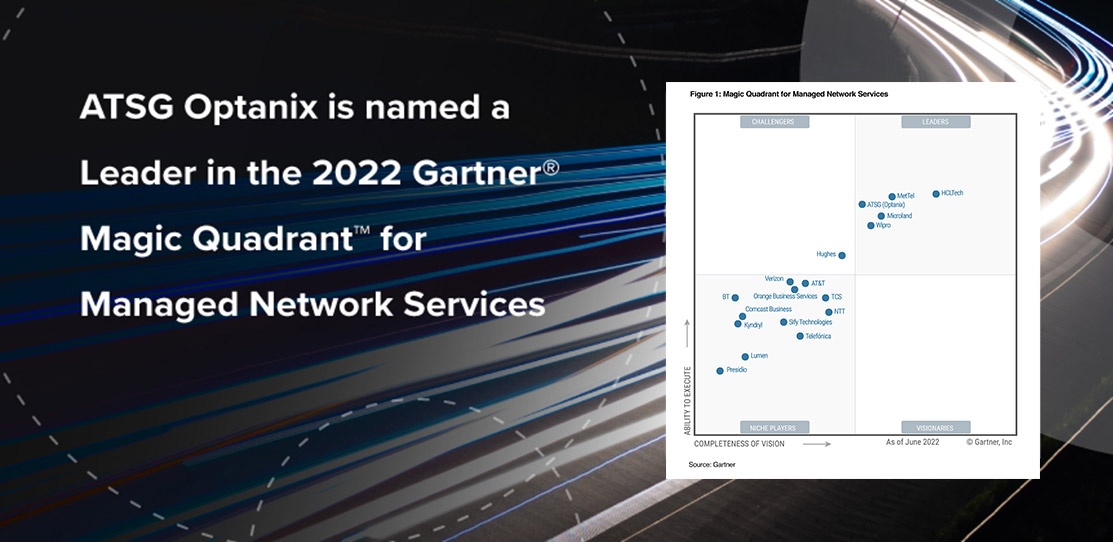
ATSG (Optanix) Named a Leader in 2022 Gartner® Magic Quadrant™ for Managed Network Services
Gartner recently published the 2022 Magic Quadrant for Managed Network Services (MNS) which identified ATSG

The Significance of a Strong Cybersecurity Culture, and How to Build One?
Over the years, it has become self-evident that various stakeholders have a set number of

The Heart of Digital Transformation – Improved Customer Experience
As businesses transit from a disruptive global pandemic, one thing is for sure; the world

How are Media and Entertainment Giants Leveraging Cloud Solutions?
It is fascinating to see how the latest technologies and digital products have “changed the

How are Cloud Computing Technologies Driving Sustainability?
Earth is the only planet in the universe known to possess life. Unfortunately, we have

How Can the Healthcare Sector Win Against Cyber Criminals?
Various cybersecurity statistics tell us that no enterprise is immune to cyber-attacks. This painful reality

Navigating Cloud Security Posture Management (CSPM) in 2023
The year 2022 has been all about the consolidation of IT infrastructures and optimizing their

Distributed Denial of Service (DDoS) Attacks a Major Cause for Concern in 2023
The year 2022 has been quite an eventful one for IT infrastructures across the globe.

