The healthcare sector has been at the forefront of responding to a devastating pandemic. As the pandemic still rages on, healthcare providers across the globe have to contend with yet another challenge, which is the rising and looming threat of ransomware attacks.
A recent report by Health Care Compliance Association (HCCA) has painted a dismal outlook for the security posture of healthcare institutions globally. As per the report, the frequency and lethality of ransomware attacks on healthcare will rise in 2022.
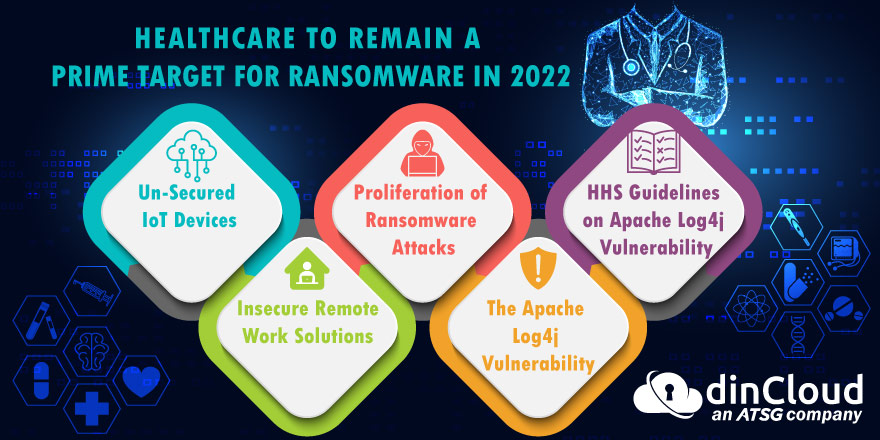
In this post, we will discuss the salient features of the HCCA report on the looming ransomware threats, and the major factors contributing to such threats.
Un-Secured IoT Devices
The HCCA report highlights the issue of un-secured Internet of Things (IoT) devices that have rapidly made their way into healthcare systems. These devices are a mix of both personally owned ones, and the ones purchase by healthcare institutions as well.
Such insecure IoT devices, especially when connected to the hospital networks in some way, act as a point of entry for cyber criminals into the network. Once inside, cyber criminals can potentially implant the ransomware with ease, and cause serious damage.
Insecure Remote Work Solutions
The trend of remote work also made its way to the healthcare sector, albeit partially. It is not remote work platforms that are causing the actual problem, rather it’s the use of loosely, or completely insecure platforms for remote access that are the threat.
Such poorly secured remote work platforms act as a major entry point for cyber criminals, as they can eventually gain access to core hospital and healthcare provider networks. The report strictly discourages the use of un-structured remote access solutions.
Proliferation of Ransomware Attacks
According to cyber security company Deep Instinct, healthcare providers will continue to remain a prized target for ransomware attacks in particular. The recent ransomware attacks on healthcare institutions, and the quick doling out of ransoms, is the major cause.
While some may argue that healthcare institutions have no other choice but to quickly cough out the ransom amount, this course of action has really emboldened cyber criminals to focus their attacks largely on institutions associated with the healthcare sector.
The Apache Log4j Vulnerability
US Department of Health and Human Services (HHS) has also highlighted the threats originating due to the infamous Apache Log4j vulnerability. While the piece of software exists in many applications, its use in medical devices and hardware is concerning.
The existence of such a vulnerability within medical hardware and devices poses a two pronged threat. Firstly, this can result in data exfiltration from and through these devices, or the planting of ransomware via this channel.
Secondly, such a threat can greatly impede the ability of healthcare institutions to provide both critical and routine healthcare to patients. In no time, this issue escalates to become one of national security, as it impacts the lives of thousands and millions.
HHS Guidelines on Apache Log4j Vulnerability
The US Department of Health and Human Services (HHS) has issued the following guidelines to healthcare institutions regarding the Log4j vulnerability:-
- Across the board implementation of the guidelines issued on this vulnerability by the Department of Homeland Security Cybersecurity and Infrastructure Security Agency (CISA).
- Implementing an elaborate review process within healthcare institutions, in the light of the resources shared by HHS and CISA, from time to time.
- Diligent monitoring of the networks of healthcare providing institutions, to point out any abnormal patterns.
- Raise the overall cyber security awareness across both the medical and IT staff of healthcare institutions.
- Maintain readiness for emergency operations, designing of procedures for such situations and putting those continuity plans into action.
- Prompt reporting of any cyber security incidents to CISA, the FBI, or both institutions.
Conclusion
Despite the looming cyber security threats in general, and ransomware in particular, healthcare institutions simply cannot afford to let their guard down. As attack vectors evolve, cyber security will have to evolve from reactive to proactive.
Adopting a proactive approach to cyber security threats is now the only viable approach towards tackling this menace. While this may not always be the case, this mindset and approach that today’s threats are un-stoppable is self defeating.
Healthcare providing institutions can immensely improve their overall cyber security posture and preparedness by adopting the guidelines laid down by the Department of Health and Human Services (HHS).
Contact dinCloud, an ATSG Company, for cloud solutions that meet some of the best international and compliance standards for data privacy as well as security.


