The role if information and digital technologies is constantly on the rise in our work as well as personal lives. While these technologies are a great help, they also have their fair share of risks that need to be understood, and then managed.
Most of the digital technologies out there have become nearly indispensable for us now. So, instead of shying away from such useful technologies, using them in a secure and productive way is a much better option.

In this post, we will be covering two technologies that play a key role in securing our digital assets. These include Cloud Security and Cyber Security. We will be covering the major similarities and differences among both as well.
Related: Strengthening Security in the Cloud
Cloud Security
This is the set of all the protocols, tools and software that work in tandem to keep your data that is stored over cloud servers safe as well as secure. This data can include even sensitive and personal information. For this reason, cloud security is really important.
Cyber Security
The area of cyber security mainly deals with securing in-house IT assets such as networks, from external threats and internal vulnerabilities. Preventing any un-authorized access to organizational networks is also part and parcel of cyber security.
Now that we have defined both Cloud and Cyber security, let us discuss how each of these is pulled off. In this whole process, you will be in a much better position to understand the similarities and differences between the two.
Related: The Cyber Security Outlook by Gartner for 2022 and Beyond
Salient Features of Cloud Security
The role of cloud computing services and solutions in enterprise operations is constantly on the rise. With this, the security related stakes are also very high. So, cloud security relies on multiple techniques to deliver a secure computing and storage environment.
Let us take a glimpse of how Cloud Security actually works, and the techniques upon which Cloud Service Providers (CSP) generally rely.
User Authentication
In the case of your data stored over the Cloud, user authentication becomes really important, and is provided by your cloud provider. Leading Cloud Service Providers (CSP) like dinCloud rely on Two Factor Authentication (2FA), before giving any access to users.
Role Based Authorization
In the case of top cloud providers like dinCloud, a single user is generally not given access to the whole data stored over the Cloud. Instead, the data and network are sub-segmented, so authorization rights are given to users based on relevance and the assigned tasks.
Related: No Better Time to Address Your Cloud Security Concerns
Data Encryption
Cloud Service Providers (CSP) like dinCloud keep your data in encrypted form. This extends to the application, network and transport layers of the cloud infrastructure. When encrypted, the data is of no useful value for the perpetrator of a cyber attack.
Periodic Data Backups
Most leading CSPs like dinCloud invest a lot in preparing, and safely maintaining the backups of your data on a regular basis. These backups of cloud hosted virtual machines are also called “snapshots”, and their frequency varies with each organization’s needs.
Related: How to Create a Robust Cyber Security Strategy?
Compliance and Regulatory Standards
In the case of cloud services, as your data is stored within the data centers of a CSP, there could be some laid down regulatory standards which need to be met. The data centers of leading CSPs comply with some of the best international standards for compliance.
How Does Cyber Security Work?
If we draw a direct comparison between these two, Cloud Security is way more complicated as compared to Cyber Security. The scope of cyber security is mainly restricted to the inner elements of the organizational network and resources, but it is also equally important.
Let us now see how cyber security works, and the major tools it leverages to pull off a secure infrastructure.
Related: Crunching the Numbers on Multi Cloud Security in 2022
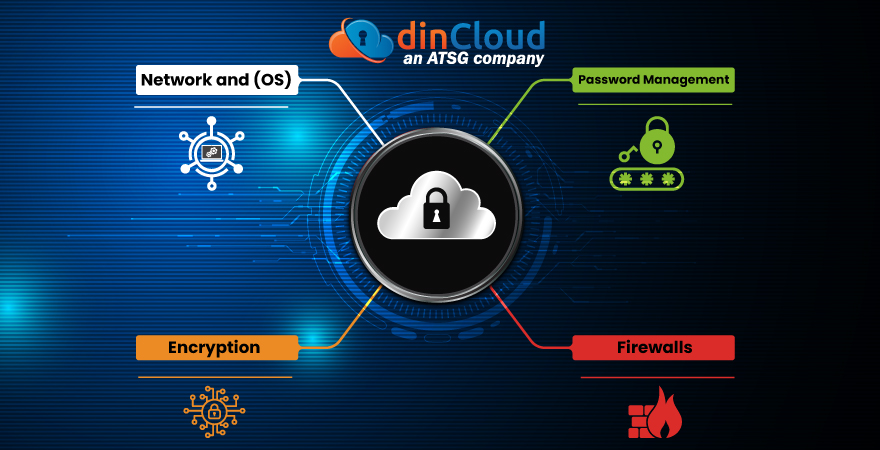
Firewalls
As the name suggests, firewalls prevent the un-authorized access, use and manipulation of data that is stored within the internal IT resources of an enterprise. These manage and control who enters the core network, and who stays outside.
Encryption
This facet of encryption is common in both cloud and cyber security. Even in the event of some unauthorized access to data, encryption makes it useless / un-intelligible for the perpetrators of the cyber attack.
Network and Operating System (OS)
Cyber security also covers other broad areas, such as protection of the internal network and the operating system (OS). The main goal is to protect the network from internal vulnerabilities and external threats.
Password Management
A strong mechanism for passwords, and their effective management also goes a long way in improving your overall cyber security posture. Passwords need to be strong, and changed on a periodic basis for maximum efficacy.
Conclusion
Both Cloud Security and Cyber Security have similarities as well as differences. The common denominator among both is the element of Security, which can never be ignored in the present circumstances.
Contact dinCloud, an ATSG Company, for highly secure and compliant cloud solutions for your enterprise.


