The Covid-19 pandemic has accelerated the trend of remote work over the past few weeks. However, the concept is not new, especially in technology driven working environments where remote work is not a barrier to productivity.
As a result of this recent crisis and the chain of events triggered by this pandemic, remote work is the new “normal” for thousands of businesses and millions of professionals. In this post, we will discuss how you can create the right balance in such a scenario.
Also Read:
- 17 Best Practices to Attain Secure Remote Work Environments
- How VDI and DaaS are Supporting Remote Work?
Challenges of Remote Work
Although we are not new to working remotely, but the concept of remote work for prolonged periods of time is surely new to most of us. Hence, this poses a unique set of challenges that are both psychological and related to cyber security.
Psychological Toll of Remote Work
In the new work from home norm, the boundaries between your professional and personal life have faded away. The premises that was previously used for sleeping, cooking meals or watching TV is also now your workplace.
This trend has posed both psychological and administrative challenges for millions of people working from home. Now, most of us are forced to juggle personal tasks in our working hours and vice versa.
Security Challenges of Remote Work
Cyber security is another area receiving a lot of attention in the new remote work scenario. Most businesses have rushed to adopt a minimal framework that enables them to connect and remain productive without showing up at the workplace.
When racing against time and low on both financial and administrative resources, cyber security may be among the last things on your mind. However, this mindset or any such oversight can have devastating consequences over time.
Also Read:
- Cloud Computing and Covid-19 – Bracing for Remote Work Scenarios
- Covid-19 and Productivity in a Prolonged Remote Work Scenario
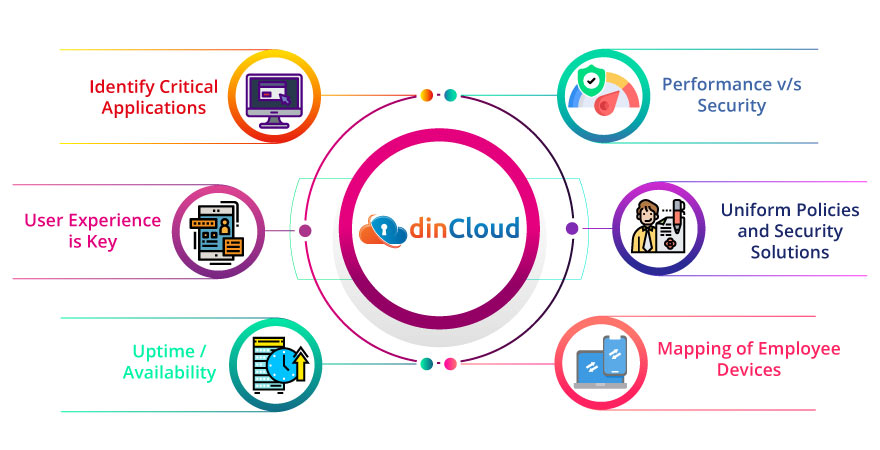
Below are a few helpful insights on how you can create the right balance between productivity and security of your remote workforce.
Identify Critical Applications
Under normal circumstances, you may have deployed a lot of applications or software for your workforce. When going fully remote, you may not have the resources to maintain the same level of app availability.
Therefore, it’s best that you identify critical applications and enterprise software that your workforce absolutely needs to manage the workflows in a seamless, productive manner. Making them available to all relevant employees should be your top priority.
User Experience is Key
Employee productivity and motivation levels are directly proportional to end user experience these days. Employees are more awake than ever about the latest remote working tools, trends and solutions in their respective industries.
You have to focus on remote work solutions that are not only productive, but also rank high in terms of end user experience. Instead of imposing remote work software on your workforce, adopt an inclusive approach and also include employee input.
Uptime / Availability
This is one factor that will play a key role in the productivity of your employees. Whatever remote work solution you deploy, ensure that its uptime is in the range of 99%. Any disruptions to workflow are negative for productivity and employee morale.
Performance v/s Security
It is obvious that you can’t compromise on security, especially when employees are working remotely. However, the way you deploy network and cyber security tools will have a direct impact on the performance of your remote work infrastructure.
Focus on security solutions that deliver the required protection from external threats and internal vulnerabilities, without creating a lot of drag on performance. If you don’t do so, most employees will end bypassing your security protocols, posing new risks.
Uniform Policies and Security Solutions
In the present remote work scenario that’s witnessing record number of cyber attacks, you simply can’t pick and choose where security protocols will apply. There should be a holistic approach to cyber security and no one should be able to bypass the security protocols.
Regardless of whether it’s an on premise solution or a cloud based service, your cyber security solution should be uniform. Secondly, its application has to be at the perimeter level so that there is minimal to no risk of unauthorized access or intrusion.
Mapping of Employee Devices
In these remote work times, your employees may be using a number of devices to access organizational data or applications. This aspect of security also needs a deeper look and strict regulation. To plug this gap, you need to map all employee devices.
This is possible once you have credentials of each device your employee will be using to access company data or apps. Outside of the mapped devices, no other device whatsoever should be allowed access to enterprise data or software.
Also Read:
- dinCloud Steps Up To Support Growing Demand For Remote Workforce In Wake Of COVID-19 Impact
- How to Manage a Long Term Work from Home Scenario?
dinCloud and Remote Work
At dinCloud, we have a highly robust, secure and reliable remote work solution in the form of our cloud Hosted Virtual Desktops (dinHVD). They are a secure and cost effective answer to all your remote work needs, including processing intensive workloads.
Contact Us for your remote work or Business Continuity needs so that dinCloud can offer a cloud solution that’s best for you, at an unbeatable price.


